Organizations Increasingly Employ Zero Trust Principles to Protect Digital Infrastructure
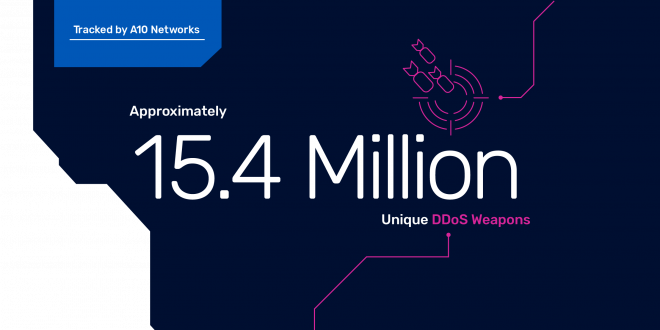
It is well-reported that the pandemic caused a spike in cyberattacks, including malware, ransomware and DDoS attacks. Threat actors have sought to disrupt not only services people rely on everyday like healthcare, education and financial but also critical infrastructure, like food supply chains, utilities and government agencies. Correspondingly, there has been a dramatic increase in the weapons that can be used to launch these attacks. In the 2H 2021 reporting period, A10 Networks security research team tracked over 15.4 million DDoS weapons in 2021. Recently, A10 Networks’ threat intelligence detailed the use of DDoS attacks to disrupt infrastructure and communications in Ukraine in February 2022 just as Russia launched its ground attack.
A10’s threat intelligence research team monitored significant advances in scope and intensity of cybercrimes.
- DDoS weapons are on the rise: 15.4 million are now tracked by A10’s security research team
- There was an increase of over 100 percent, year-over-year, of more obscure potential amplification weapons, including Apple Remote Desktop (ARD), which was used in the Russia-Ukraine conflict
- Attackers have leveraged the now well-known Log4j vulnerability; more than 75 percent of Log4j scanners originated in Russia
These, and other trends, are included in the 2022 A10 Networks DDoS Threat Report, which provides detailed insights, including the origins of DDoS activity; the growth of DDoS weapons – the computers, servers and IoT devices that can potentially be used in DDoS attacks – and botnets; the role of malware in the propagation of DDoS weapons and attacks; and the steps organizations can take to protect against such activities.
Organizations Must Act Now – Employ Zero Trust Principles
On March 21, 2022, the Biden-Harris Administration issued guidance urging U.S. organizations to act quickly to protect against cyber attacks and state-sponsored cyber warfare given the ongoing Russia-Ukraine conflict.
The guidance, while aimed at U.S.-based organizations, details a sense of urgency for organizations globally to reevaluate their security posture. Employing Zero Trust principles can not only protect networks but also ensure that they are not being used to launch attacks. A10’s security-led solutions for DDoS protection, TLS/SSL inspection of encrypted traffic and application delivery security capabilities can provide identity-based and context-based Zero Trust policies for specific enforced access.
“Recent events underscore the often devastating impact that cyber attacks have on governments and businesses around the world. A10 Networks tracks the origins of DDoS weapons activity, in addition to other attack vectors, in order to arm customers with useful threat intelligence. This is a critical component of a Zero Trust framework to help organizations better anticipate and mitigate cyber attacks, and also ensure networks are not inadvertently being weaponized,” said Dhrupad Trivedi, president and CEO of A10 Networks.
As a testament to A10’s technology innovation, Frost & Sullivan recently evaluated A10’s DDoS protection solutions, along with several other vendors, and awarded A10 the “2021 Frost & Sullivan Customer Value Leadership award for global DDoS mitigation, for excellence in best practices.”
In addition, to further support our customers’ cybersecurity needs and contribute to global solutions to cyber threats, A10 recently joined the Microsoft Intelligent Security Association (MISA), which is an ecosystem of independent software vendors and managed security service providers that have integrated their solutions to better defend against a world of increasing threats. More detailed results are available in the full 2022 A10 Networks DDoS Threat Report.
Follow them on Social Media
- Visit A10 Network blog
Connect with us on Facebook and LinkedIn and Twitter

The Broll who always got your back online!